It’s easy to lose your cryptocurrency without good security measures in place.
Keeping your Ethereum or cryptocurrency secure should be the highest priority for any investor looking to enter the market. It should be noted that most users would claim to be security conscious when it comes to crypto, however it’s easier to lose your coins than people realize.
There are a few crucial steps you must take if you want to keep your Ethereum safe or any other cryptocurrency for that matter. This guide will help to outline the major security issues that can take place and how to lock your coin stash tight.

1. 2FA and Crypto
2 Factor Authentication is one of the greatest security revolutions to happen in the last 10 years. If you’re unfamiliar with what 2FA is, simply put it places a block on your account that cannot be removed unless you give the account access via a mobile device. Think of your cell phone like a key to access an account with 2FA. If you’d like to learn more about 2FA, check out this great article outlining it here .
How do you setup 2FA ?
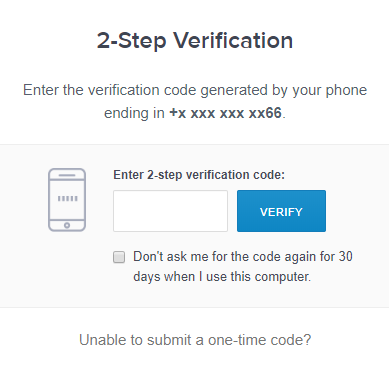
There is two ways of setting of 2FA for most cryptocurrency exchanges. You can choose to receive a text message that provides a one time code you enter to access your account or you can use the Google Authentication App. There is benefits to each type of 2fa, however one of the two has a large security hole that has been exploited quite often recently.
Why you should not use SMS based 2FA
In early 2018, a ton of crypto investors lost their funds on exchanges due to a widespread social engineered hack in 2FA. Hackers are finding out peoples cell phone numbers and personal details of the crypto investor they are targeting. Once they acquire enough info, they will call that individuals cell phone provider to get their number ported onto their own device. So you lose your phone number and they now have access to ANY 2FA you have setup via SMS verification. This is why we recommend sticking with the Google Auth App.
An example of a Coinbase SMS verification screen
Why you should use the Google Authentication App
The Google Authentication app is great because it generates random numbers every 15 seconds or so, so it’s nearly impossible for a hacker to exploit this method of 2FA, unless they have your phone in hand. The downside to this is if you lose your device or it becomes compromised, you will also lose access to your Google Authentication App. However, your account would still be secured in theory and after Google does some verification, you can recover the Google Authentication account.
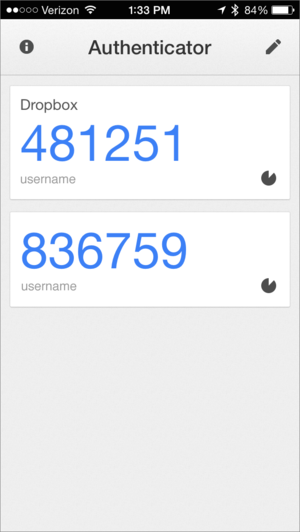
The Google Authentication App
2. Protect your wallets private key
This is a very obvious security measure you should take, but there is still people in the world who don’t understand the difference between their public and private key. We are sympathetic to this confusion as they do look very similar and without an explanation you may not understand the risk of giving it away. Many sites trying to steal your precious cryptocurrency will ask for these details as well.
Please remember that NO ONE will ever ask for your private key if they have good intentions; only thieves will be asking for your private key. If an exchange is asking you to upload your private key or 24 word recovery phrase, leave that site immediately and never look back.
What is a 24 word recovery phrase?
A 24 word recovery phrase is 24 words that are provided to you upon setting up your wallet. These 24 words will allow you to recover your wallet no matter what happens (accidental uninstall, broken hardware, etc). Be VERY careful with these words as they can give access to your wallet to anyone that has them, bypassing any security you have setup. This is the backdoor to accessing a crypto wallet and should be treated with the same care as your coins.
Where should I store my 24 word recovery phrase?
The key should be stored somewhere safe and offline it possible The reason you want to store the key offline is to ensure if your hardware is compromised by a hacker, they won’t have access to your 24 Word Key and will not be able to access your 2FA enabled wallet.
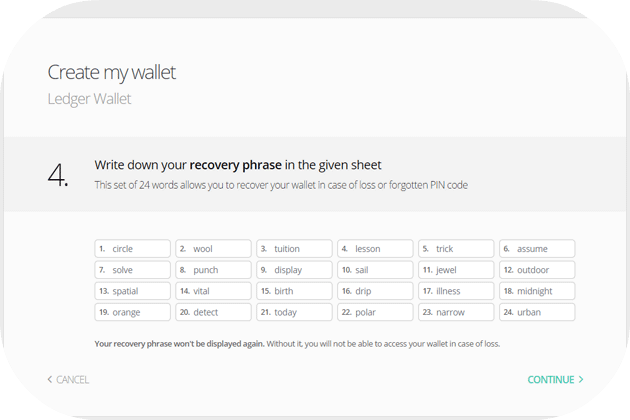
An example of a Ledger Hardware Wallet 24 word phrase key.
3. The best crypto wallet, period.
The best wallet for cryptocurrency is a Ledger Nano S, without a doubt. The reason being is the Ledger is a hardware wallet which means you can’t open any of your cryptocurrency wallets unless the Ledger is plugged into your computer. This ensures that if a hacker gains access to your computer, it is impossible for them to send your coins because they don’t have access to the Ledger Nano S. However, if your 24 word recovery phrase is compromised, they can still access the wallet without the ledger, so keep it safe !
Where can I buy a Ledger Nano S ?
You can buy them on Amazon at a reduced price or on the Nano S website. Be wary when buying off Amazon that you’re purchasing from a trusted seller.
4. Use your head
If something seems fishy, it probably is. Don’t send your coins to anyone you don’t trust. Don’t visit websites that seem suspicious or have a URL you don’t recognize. Make sure you’re always on the URL you intended to visit and not some variation meant to fool you into handing your info over. There is nobody in the world who wants to give you free cryptocurrency, so anything you see that suggests so should be avoided at all costs. At the end of the day, crypto is an asset you have protect yourself and if you’re not capable of doing so, you probably shouldn’t invest. There is no recourse if you lose your coins, so please ensure you have protected yourself in every way possible. Even some of the biggest crypto gurus have had all their coins stolen.